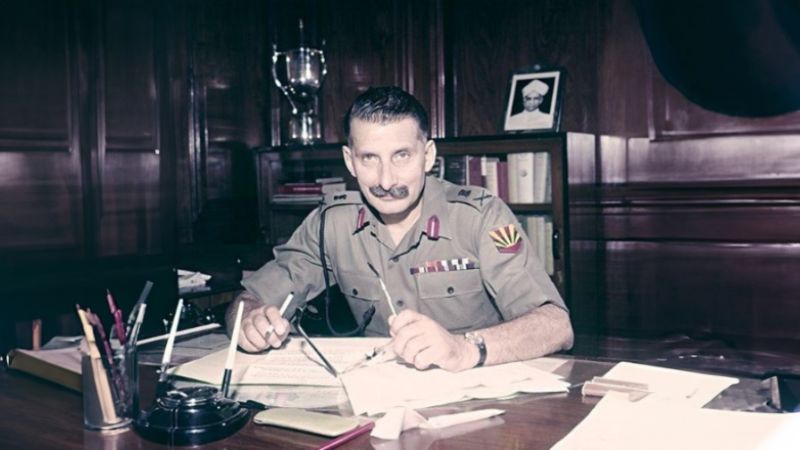
Sam Bahadur 2023: The Tale of Remarkable Valor
Get ready for a cinematic journey through history with ‘Sam Bahadur.’ This highly-anticipated biographical war drama delves into the life of India’s first Field Marshal,… Read More »Sam Bahadur 2023: The Tale of Remarkable Valor